Superfish Spyware Also Available for iOS and Android
On February 20, 2015 by Jonathan ZdziarskiFor those watching the Superfish debacle unfold, you may also be interested to note that Superfish has an app titled LikeThat available for iOS and Android. The app is a visual search tool apparently for finding furniture that you like (whatever). They also have other visual search apps for pets and other idiotic things, all of which seem to be quite popular. Taking a closer look at the application, it appears as though they also do quite a bit of application tracking, including reporting your device’s unique identifier back to an analytics company. They’ve also taken some rather sketchy approaches to how they handle photos so as to potentially preserve the EXIF data in them, which can include your GPS position and other information.
To get started, just taking a quick look at the binary using ‘strings’ can give you some sketchy information. Here are some of the URLs in the binary:
https://sdk.appsflyer.com/install_data/v3/id%@?devkey=%@&device_id=%@ http://track.appsflyer.com/api/v%@/ios%@?app_id=%@&buildnumber=%@ https://et.kissmetrics.com/m/trk https://trk.kissmetrics.com
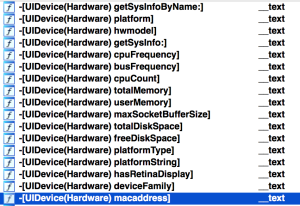
In fact, Superfish seems to be very interested in your device, and has code in it to determine your mac address, free disk space, and even how much memory you’re using.
So any anonymous user using the application runs the risk of being tracked using a unique identifier that’s possibly tied to their device’s mac address, without any warning or privacy policy from Superfish. Last time I checked, tracking users in this fashion was against App Store rules, however Apple seems to be turning a blind eye to it lately, as Google, Whisper, and a host of other apps have been caught red handed doing the same thing, with complete impunity. Apple’s apathy in allowing apps to track you (in spite of their doing away with the UDID) has caused behind-the-scenes tracking to be relatively ubiquitous among iOS applications.
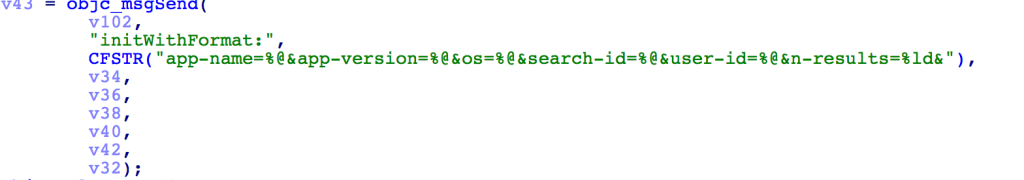
As it happens, every search you perform using their API appears to include the unique user identifier they’ve created without your knowledge:
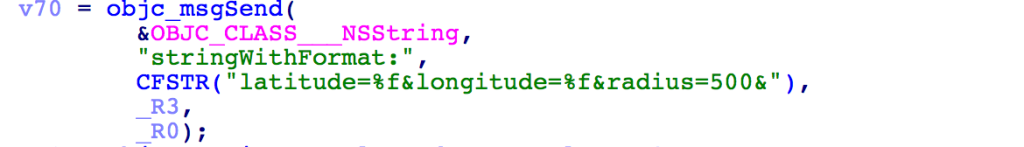
But wait, there’s more! If location services are enabled (in iOS, you have to provide permission; I’ve no idea about Android), then apparently your GPS position is also sent back to the server.
It is unclear if these features are currently enabled in the iOS or Android versions of the application, but it appears as though support for acquiring and reporting your position is at least there, within their SFLocationAPI class.
In addition to mining your device for identifying information, it appears as though the image selection mechanisms use ALAssetsLibrary and friends, which can later be used to extract the EXIF data out of an image in the photo album, which could include GPS coordinates the photo was taken at. So even if you never provided the application itself permission to use the GPS, it may not matter, if the image is being sent up the pipe with all of the EXIF data attached to it. In my opinion, Apple really should ask the user for permission before allowing applications to access the raw metadata in JPG images.
It seems Superfish went out of their way to avoid using the correct method to select an image from your photo album (UIImagePicker), and instead decided to use a technique that could allow access to underlying image metadata most users aren’t aware gets stored.
When taking photos, Superfish has also gone to great lengths to avoid using Apple’s standard interfaces for taking pictures, and instead use low level interfaces and functions that can allow access to the underlying metadata of an image.
Conclusions
In the brief time I spent analyzing Superfish’s image search app, it seems that the same theme of blatant disregard for the user’s privacy and sketchy, sneaky nonconventional code is prevalent in more than just their bundled Lenovo software. That’s it for now, I’ll take a more in-depth look at the code later and update as necessary.
There’s no telling exactly what Superfish is and isn’t doing with what personal data. I guess the question really is whether or not you trust a company that Homeland Security is now warning you against.
Archives
- May 2026
- April 2026
- February 2026
- December 2025
- November 2025
- October 2025
- August 2025
- July 2025
- March 2025
- December 2024
- March 2024
- July 2023
- May 2023
- February 2023
- December 2022
- November 2022
- July 2022
- May 2022
- March 2022
- January 2022
- December 2021
- November 2021
- September 2021
- July 2021
- December 2020
- November 2020
- March 2020
- September 2019
- August 2019
- August 2018
- March 2018
- March 2017
- February 2017
- January 2017
- November 2016
- October 2016
- July 2016
- April 2016
- March 2016
- February 2016
- June 2015
- March 2015
- February 2015
- December 2014
- November 2014
- October 2014
- September 2014
- August 2014
- July 2014
- June 2014
- May 2014
- April 2014
- March 2014
- January 2014
- October 2013
- September 2013
- June 2013
- May 2013
- April 2013
- December 2012
- May 2012
- September 2011
- June 2011
- August 2010
- July 2010
- May 2010
- April 2010
- February 2010
- July 2009
- May 2008
- March 2008
- January 2008
- June 2007
- August 2006
- February 2006
Calendar
| M | T | W | T | F | S | S |
|---|---|---|---|---|---|---|
| 1 | 2 | 3 | ||||
| 4 | 5 | 6 | 7 | 8 | 9 | 10 |
| 11 | 12 | 13 | 14 | 15 | 16 | 17 |
| 18 | 19 | 20 | 21 | 22 | 23 | 24 |
| 25 | 26 | 27 | 28 | 29 | 30 | 31 |